如今,在数字化转型、工业物联网以及人工智能和机器学习等新兴技术的推动下,IT与OT环境正加速融合。这对过程行业而言究竟意味着什么?
随着IT与OT的深度融合,物理世界与数字空间的界限日益模糊,催生了全新的安全隐患。集成安全不再是“锦上添花”,而是“势在必行”。曾经彼此孤立的系统,如今正日益紧密互联,而它们在设计之初,并未考虑到要在清晰设定的网络安全分区和受控数据通道中运行。本质上,这意味着关键基础设施和工业运营可能更容易受到网络攻击,进而影响生产效率、产品质量,甚至生产安全。
什么是IT/OT安全?
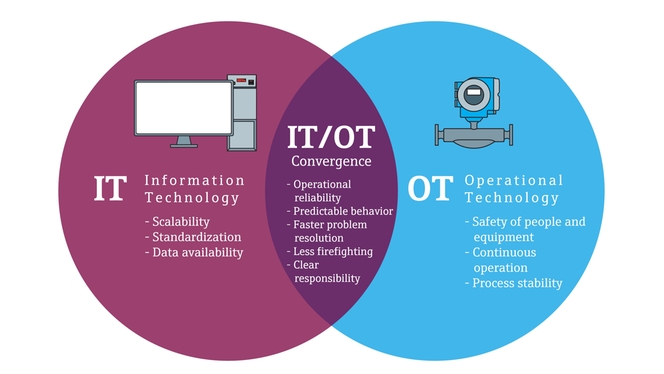
传统上,IT安全侧重于保护数据和信息系统,确保其机密性、完整性和可用性。防范计算机、网络与服务器遭受入侵、恶意软件攻击及未授权访问;而OT安全性则侧重于保护用于监测、控制和测量物理过程与设备的软硬件。其主要目标是确保工厂内物理设备的安全性与持续可用性。
如今,物理空间与数字空间的互联程度不断提升,一种新的IT/OT安全概念应运而生,即通过实践与技术,保护数字信息系统(IT)与物理过程控制系统(OT)免受网络威胁。随着数字传感器与工业物联网技术的应用,过程行业中数字与物理之间的界限逐渐模糊,因此,我们不仅要做好物理防护,更要保障仪表设备的网络安全。
过程行业中网络安全的重要性
在过程行业中,IT/OT安全不再局限于数据保护,更关乎保障工厂正常运行、守护公共安全的关键运营。微小安全漏洞,就可能引发生产停机、设备损坏、环境危害,甚至危及人身安全。随着系统互联范围扩大、监管要求趋严,保障IT/OT系统安全,必须成为企业的核心要务,其原因如下:
工业4.0的发展与实时安全风险管理的需求
最近,工业4.0推动了互联系统、自动化与数据型过程的发展。但互联程度的提升也意味着面临更多网络威胁。传统的定期风险评估已无法跟上当今动态环境的步伐。实时安全风险管理可让企业在威胁发生时即时检测、评估并响应,缩短停机时间,保障关键运营。
通过持续监测IT和OT网络,企业可以及时发现异常和漏洞。实时数据支持动态风险分级,确保资源优先投入核心问题。此方案还可以结合自动化警报和预设响应工作流程,加速恢复,显著降低运营影响。
IEC 62443系列标准强调,在工业自动化与控制系统全生命周期内持续进行风险管理,以此构建网络韧性的基础。
在数字工厂实现网络韧性
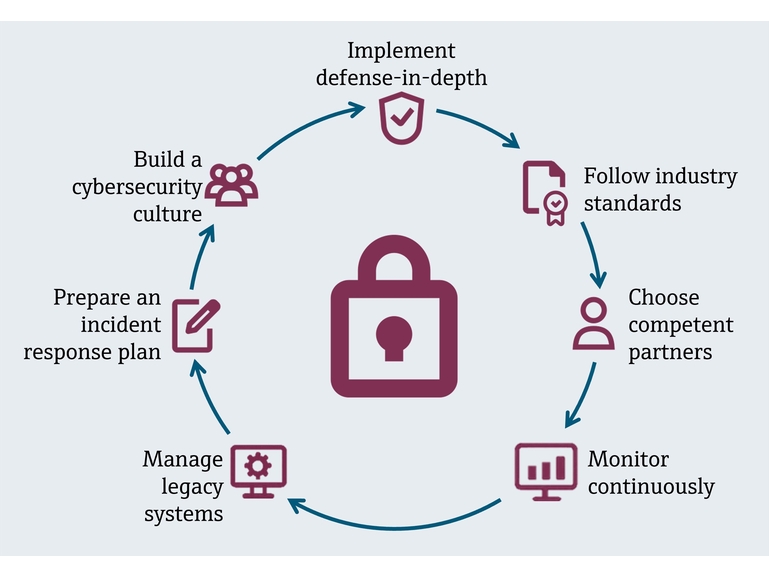
网络韧性并非一蹴而就,而是持续的过程。在日益互联的世界中,这一举措能够增强运营连续性,并保护关键基础设施。确保工厂网络韧性,能让运营在遭遇网络安全事件后快速抵御冲击、恢复运行,且不影响生产安全或生产效率。为构建工厂网络韧性,我们建议采取以下措施:
- 实施纵深防御:在IT和OT网络中部署多层安全措施,如防火墙、入侵检测、网络分区以及严格的访问控制。
- 遵循行业标准:采用IEC 62443和NIST网络安全框架等标准,确保合规性并践行最佳实践。
- 选择可靠的合作伙伴:选择具备认证安全开发生命周期的供应商。这能确保部件从设计阶段便内置安全能力,并实现全生命周期管理。
- 持续监测:使用实时监测和威胁检测工具,以便掌握全局并快速响应异常情况。
- 管理传统系统:在无法进行补丁更新的情况下,采用网络隔离、应用程序白名单等补偿性管控措施。
- 制定事件响应计划:明确职责、上报流程和恢复步骤,并定期演练保障应急能力。
- 构建网络安全文化:培训员工,促进IT与OT团队协作,定期进行风险评估,以保护关键资产。
安全互联:网络韧性的基础
唯有底层基础设施安全可靠,才能实现网络韧性和实时风险管理。在过程行业中,IO-Link、Ethernet-APL和Bluetooth®蓝牙等连接协议构成了智能自动化的核心基础,实现了现场设备、控制系统和企业网络之间的无缝数据交换。
然而,这些协议不仅仅是为实现互联;如果缺乏严格的安全实践支持,它们也可能为潜在网络威胁敞开大门。因此,选择网络安全成熟度高的供应商合作,是保障工厂安全的关键。设备身份、可信数据源以及传感器和执行器层面的受控访问等要素,直接影响着PLC、DCS、MES等上层系统的效能。成熟的供应商能确保核心防护措施从设计之初就已内置系统中。
网络安全的防护强度取决于最薄弱的连接节点,因此现场级通信必须以高标准严要求来实施。选择遵循IEC 62443等标准、采用全生命周期安全理念的供应商,有助于确保设备级防护措施夯实全厂的安全根基。携手将稳健安全措施融入研发实践的合作伙伴,企业可放心推进数字化转型,避免转型带来新的安全风险。